Explained: what is End-To-End Encryption?
Home » Security » Explained: what is End-To-End Encryption?
You’ve probably heard of End-to-end Encryption before. Especially if you use Whatsapp regularly. Messages and calls are end-to-end encrypted so no one outside the chat can read or listen to them. Sounds good. But how does that actually work and in what environments is it used? We will be covering it for you in this article.
End-to-end Encryption
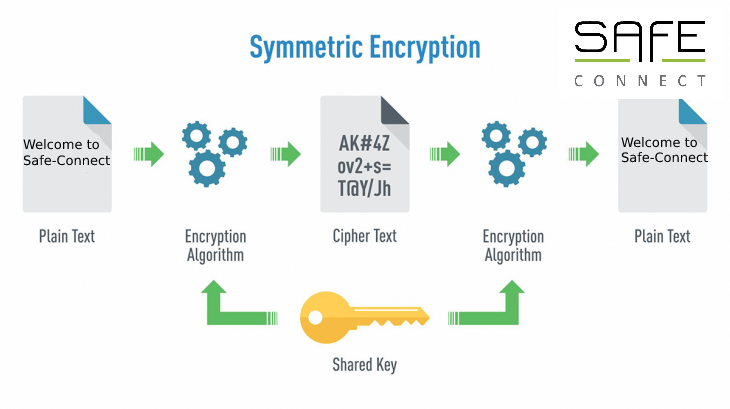
End-to-end encryption (E2EE) is a method of enabling secure communications. It prevents third parties from accessing data while it is being transferred from one end system or device to another. With E2EE, data is encrypted on the sender’s system or device, and only the recipient can decrypt it. Unlocking as a recipient is done automatically. While the message “travels” with the digital lock to its destination, it cannot be read or manipulated by an Internet Service Provider (ISP), a hacker, the server, or any other entity or service. The latter leads to controversy, which we will discuss further in a moment.
What is it used for?
End-to-end encryption is used when data security is necessary, such as in the financial, healthcare and communications industries. The technology is often used to help companies comply with data protection and security laws and regulations.
For example, an electronic point-of-sale system vendor would include E2EE in its offerings to protect sensitive information, such as customer credit card information. With E2EE, a retailer can also comply with the Payment Card Industry Data Security Standard (PCI DSS). This standard states that card numbers, magnetic stripe data and security codes must be kept in a secure environment. That way, you can buy your sandwich in a secure manner!😉
Protecting our data or a communication tool for criminals?
Many popular messaging service providers use end-to-end encryption, including Facebook, WhatsApp and Zoom. These providers have faced controversy surrounding the decision to adopt E2EE. The technology makes it harder for providers to share user information from their services with authorities and potentially provides private messaging to people involved in illegal activities.
In a nutshell
Like any good technology, it can be abused. For ordinary users, it generally provides better security. Certainly companies with sensitive information benefit from using encrypted information exchange.
Not sure if your business is adequately secured?
You are more than welcome to contact us. During an initial meeting we will discuss the situation and possible solutions. Our security experts are always ready to help you!
Contact us